An Israeli medical facility and an LGBTQ website are the latest targets of a group affiliated with the Islamic Republic calling itself “Black Shadow.”
By Erin Viner
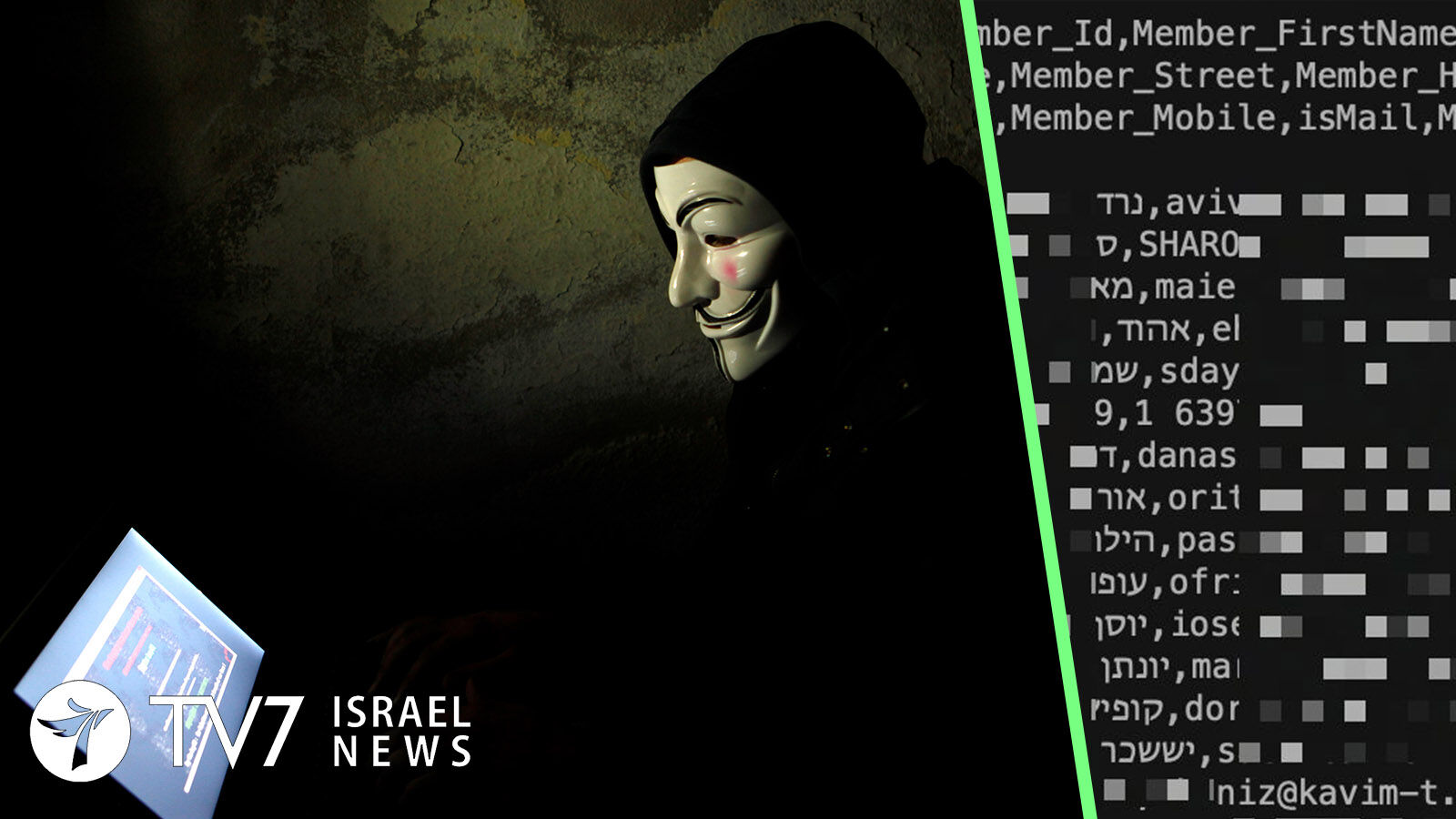
The hacking cell released personal details of tens of thousands of Israelis twice yesterday, after earlier demands for ransom were not met.
Last night the group uploaded what it claimed were complete medical records of 290,000 Israeli patients from the Machon Mor institute. The documents reportedly include the results of blood tests, CT scans, ultrasounds, colonoscopies and additional procedures, as well as patient requests to their physicians.
Earlier on Tuesday, the hackers published on the Telegram messaging app personal data of Israelis who use the Atraf LGBTQ dating app and nightlife guide – which was said to contain the names, locations, HIV status and other sensitive information about the clientele.
Yesterday’s crimes follow Black Shadow’s initial attack last Friday, when it breached the Israeli CyberServe web hosting company that provides servers and data storage for other sites. In addition to Atraf, other affected websites reportedly include the Kavim and Dan public transportation companies, the Pegasus travel agency and the Israeli Children’s Museum.
The ransom demand came on Sunday, when the group issued a statement, “If we have $1 million in our [digital] wallet in the next 48 hours, we will not leak this information and also we will not sell it to anybody.”
A warning in poor English was posted Tuesday during the publicly release of the Machon Mor and Atraf data, reading, “48 hours ended! Nobody send us money. This is not the end, we have more plan.”
CyberServe, which acknowledged this past weekend that it was dealing with “an Iranian cyber terror event,” denied conducting negotiations with Black Shadow, although the group insists it spurned the company’s lesser offer of $500,000. Israel’s National Cyber Directorate revealed on Sunday that the firm was previously cautioned over its vulnerability to attacks.
“Israeli citizens are experiencing cyber terrorism,” Israel Internet Association Director Yoram Hacohen told the Ynet news agency, saying, “This is one of the most serious attacks on privacy that Israel has ever seen.” He also maintained that Telegram bears at least partially responsible for the incident and called on tech companies to take action to prevent the leaking of private information on their platforms.
“Under no circumstances should you submit to the demands of the attackers,” he stressed, underscoring that, “There is no guarantee that if the amount is paid the information will not be published; and more importantly such a surrender will lead to further and increased attacks due to what is perceived by them as an achievement.”
Calling on the government to use legal and technological means to remove damaging online information, the Internet Association Director said, ““What needs to be done now is to refine online safety and privacy regulations and provide all the support, physically and mentally, to those about whom information has been revealed.”
Black Shadow previously hacked the Israel’s Shirbit Insurance Company in December 2020. The group claimed to have sold the personal data of the company’s clients on the dark web after its refused to pay a $1 million ransom.
Meanwhile, a separate group calling its “Moses Staff” is also claiming that it hacked into multiple Israeli companies yesterday. The targets reportedly include the HGM Engineering, David Engineers and Ehud Leviathan Engineering firms.
Moses Staff was already on Israel’s radar after it published photographs of Defense Minister Benny Gantz it claimed to have acquired from military servers amid a cyberattack on hundreds of other websites in October.
A criminal operating under the name “Sangkancil” published personal data of 7 million Israeli citizens on Telegram and online hacking forums in September purportedly stolen from the CITY4U online website used to pay municipal taxes, fines and utilities; including identity cards, tax receipts and driver’s licenses.
Israel and Iran are believed to be engaged in a covert “shadow war allegedly involving cyber and military attacks on the other side, particularly on the high seas.
Just last week, Tehran accused Jerusalem and Washington of responsibility for a major cyberattack caused major disruption to gas distribution in the Islamic Republic last week.
The Ayatollah regime has also blamed Israel for numerous incidents it said were designed to sabotage its nuclear development program, including last year’s assassination of atomic scientist Dr. Mohsen Fakhrizade, a fire at the Natanz facility in July 2020, and the Stuxnet computer virus – widely believed to have been developed by Israel and the US – that affected centrifuges used to enrich uranium struck the same facility in 2010.
According to report by Microsoft, Israel is listed as the 7th most targeted country in the world for cyberattacks, with the number of attacks attributed to Iran quadrupling. The Islamic Republic has also reportedly stepped up attacks in the cybersphere against the United States and member countries of the European Union.